America created cyberspace in its own image—free, open, decentralised, distributed, and self-governing. If the Internet had been created in China or Russia, its architecture would have been very different.
Unfortunately, its very openness and freedom have become the source of its vulnerabilities. Authoritarian nations find the freedom of cyberspace very threatening. They build firewalls to protect their societies from exercising freedom. For geopolitical reasons they also use cyberweapons to attack others.
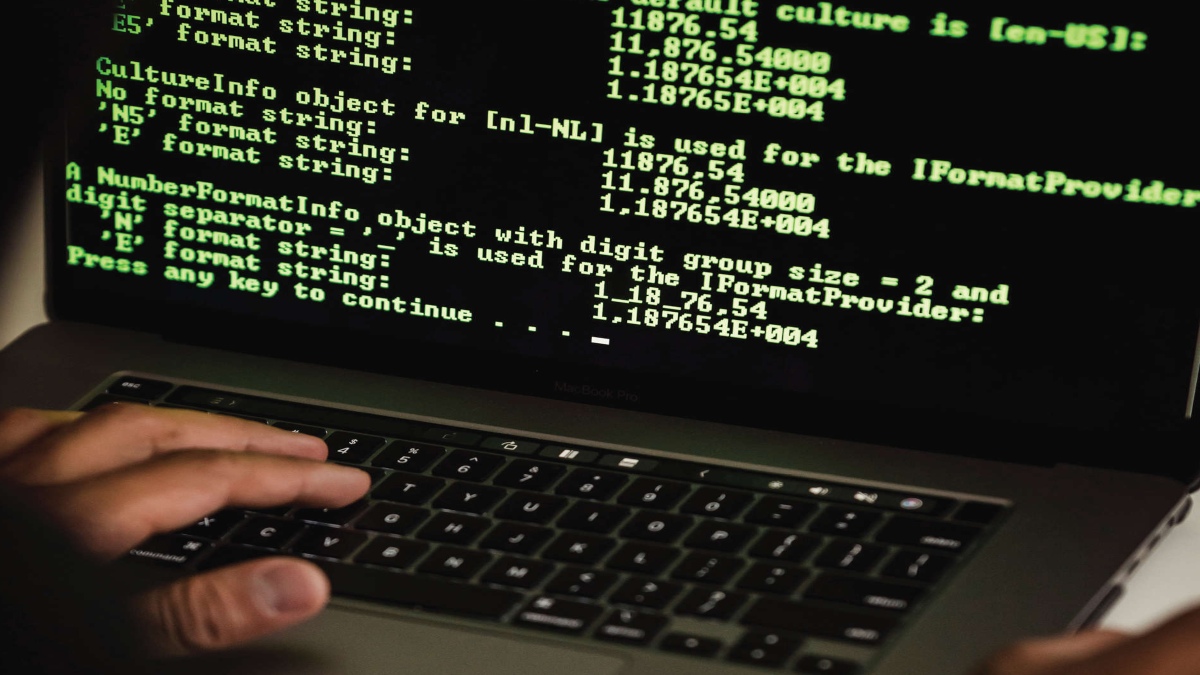
A most attractive feature of cyberspace is that its entrance threshold is so low that an ingenious self-taught person could create apps and new platforms, and become rich; or become a hacker and get into infrastructure, financial, or military systems without leaving a trace. Rogue states and well-organised digital terrorist groups use footloose hackers to steal intellectual property, and pry into diplomatic and strategic plans.Cybersecurity attacks are unobtrusive, stealthy, and insidious. There are no rules of the road to protect cyberspace, the domain into which all our activities, military, economic, commercial, political, and cultural, are being done now. Power grids, financial systems, defense networks could be brought down by not only hostile states but also the non-state actors acting alone, or in collusion with their state governments. Last October a cyber attack shut down the electrical grid of Mumbai, India’s financial capital, plunging millions into darkness. The New York Times suggested that it was a Chinese cyber-attack as a warning that China could not only fight India in the Himalayas but also in its financial hub.
The 7 May ransomware attack on Colonial Pipeline, one of America’s largest fuel suppliers, was carried out by a criminal hacking group DarkSide’s affiliate that crippled its computer system for which it had to pay the ransom in cryptocurrency, 75 Bitcoin, or nearly $5 million, according to media reports. Cryptocurrency based on Blockchain technology is a possible future for global finance. Ransom in cryptocurrency cannot be traced at present.
One of America’s most precious assets, intellectual property, is under constant threat. Chinese hackers have been accessing the designs of some major U.S. weapon systems to modernize their military. Perpetrators conceal their location due to the anonymous nature of the Internet, which makes the attribution of cyberattacks problematic. But technology is being developed to locate perpetrators. A few years ago, Mandiant, an American computer security company, was able to pinpoint that a unit of the People’s Liberation Army, located in Shanghai, had “systematically stolen hundreds of terabytes of data” from American corporations, organizations, and government agencies.
They stole “product blueprints, manufacturing plans, clinical trial results, pricing documents, negotiation strategies and other proprietary information from more than 100 of Mandiant’s clients, predominantly in the United States.”
But what can be done with hackers if they originate from Russia, North Korea, or China? The Commission on the Theft of American Intellectual Property, an independent commission, said in its March 2021 report that “IP-intensive industries support more than 45 million U.S. jobs. IP theft costs the U.S. economy hundreds of billions of dollars annually and reduces U.S. companies’ R&D investment and innovation.”
China continues to be the largest origin of IP theft today, a situation that has not changed since the Commission’s first report in 2013 when it said, “Intellectual Property (IP) theft needs to have consequences, with costs sufficiently high that state and corporate behaviour and attitudes that support such theft are fundamentally changed.” Its most intriguing recommendation included that “companies that experience cyber theft ought to be able to retrieve their electronic files or prevent the exploitation of their stolen information.” And furthermore, the report recommended, “both technology and law must be developed to implement a range of more aggressive measures that identify and penalise illegal intruders into proprietary networks….”
The National Security Agency conducts surveillance under the authority of the Foreign Intelligence Surveillance Act. It collects metadata from telephone companies and internet data from Internet Service Providers. It watches the cross-border data flow. With so much data collected through its surveillance power, the NSA should have known through its Early Awareness System about the DarkSide’s ransom attack before it occurred. One would think that Silicon Valley tech wizards should have developed foolproof encryption to protect the nation’s data. But they haven’t done it yet.
Cyberspace, in the ultimate analysis, is nothing but data. Data is power, as Dartmouth Tuck School’s Dean Matthew Slaughter and David McCormick of Bridge Associates, argued in Foreign Affairs.
With 5G technology and the ‘Internet of Things’ that would turn everything into a networked object, data would expand exponentially. They say data is “non-rival” in the sense that “it can be used simultaneously and repeatedly by any number of firms or people without being diminished.” True, but how dangerous in practical terms? Just consider: The Pentagon spends hundreds of millions of dollars of taxpayers’ money in R&D for the development of advanced defense systems, which comprises of nothing but data. If data is “non-rival,” the Pentagon shouldn’t worry when hackers copy the weapon design system based on which China could develop a competitive advanced defense system, saving millions of dollars and years of research and development, and pose a threat to America. Pfizer and Moderna vaccine patents are categorised under “non-rival” data, but they wouldn’t share with anyone.
Cyberspace has been called the fifth domain (land, air, water, space, and now cyberspace) for the protection of which the United States established Cyber Command, the Pentagon’s offensive cyber force that Trump elevated in 2017 to a separate unified military command to strengthen cyberspace operations.
America like India and other technologically advanced nations has become a data nation. Data gives us power but it creates vulnerabilities of which the DarkSide and Mumbai attacks gave us a foretaste. Who would set the new world order in the digital age? Techno-autocratic nations like China and Russia or the world’s democratic nations, the US, Japan, India and others?
Narain Batra is the author of the forthcoming book, ‘Jawaharlal Nehru to Narendra Modi’. He is professor of communications and diplomacy at Norwich University, Vermont. The views expressed are personal.
Cyberspace, in the ultimate analysis, is nothing but data. Data is power, as Dartmouth Tuck School’s Dean Matthew Slaughter and David McCormick of Bridge Associates, argued in Foreign Affairs. With 5G technology and the ‘Internet of Things’ that would turn everything into a networked object, data would expand exponentially. They say that data is ‘non-rival’ in the sense that ‘it can be used simultaneously and repeatedly by any number of firms or people without being diminished’.